Tested on OpenBSD 6.8
NOTE (2023-07-22): the Accelerated Processing Unit (APU) platform is end-of-life. This article may need updating, though many principles still apply. Proceed with caution.
Consumer routers are riddled with security problems. Between 1999 and 2017, researchers disclosed 600 Common Vulnerabilities and Exposures (CVEs) for router software—and those represent only the public vulnerabilities. The paper “So You Think Your Router Is Safe?” addresses this subject well.
Faced with this reality, and as someone who’s caught the OpenBSD bug (or pufferfish, same difference), I decided to build my own router. Here’s how I did it.
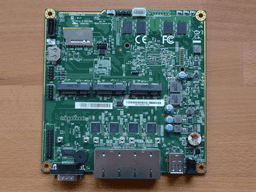
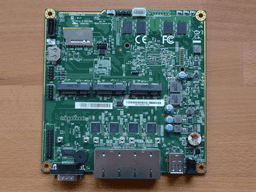
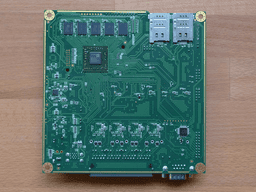
To buy an APU4D4 or similar, visit PC Engines. Their boards come with coreboot preinstalled and the experience has been great.
Include a USB to DB9F serial adapter in your order, as you’ll need it for installation.

Consult the manual for assembly instructions.
Download, verify, and flash the amd64 image that includes the file sets
(installXX.img) to a USB drive. OpenBSD’s FAQ covers
this.
Connect to the serial port. I run OpenBSD on my laptop, so I use
cu(1) for serial connections. The user
must belong to the dialer group to use
cua(4) devices.
Display the current user and their groups with
id(1).
$ id
Add the user to the dialer group if necessary with
usermod(8).
# usermod -G dialer [user]
Finally, connect to the serial port. This specifies the line to use
(-l) and the baud rate (-s). The APU4D4 requires a baud rate of
115200.
$ cu -l cuaU0 -s 115200
Remember to enter this at the boot prompt afterward to configure the serial connection. The installer sets these later.
boot> stty com0 115200
boot> set tty com0
boot> boot
From here, the FAQ provides enough information to complete the installation. Check the documentation for the relevant architecture. In this case, consult the notes on amd64.
Complete the usual tasks (read
afterboot(8), check system mail,
etc.). After that, you need to implement several components:
pppoe(4).You can also add these components:
veb(4) with good results.unbound(8), see
Creating a DNS sinkhole with Perl and unbound(8).home.arpa, see Local authoritative DNS on OpenBSD using
dhcpd(8) and unbound(8).Always give official OpenBSD documentation preferential treatment and cross-reference it when using unofficial documentation. Keep it simple and avoid changing settings unless you understand what they do.